Mike Rogers Is Ready To Serve
Our big problems need real solutions. Join Mike’s team to get America back on track.
"*" indicates required fields

Our big problems need real solutions. Join Mike’s team to get America back on track.
"*" indicates required fields
Michigan’s future is at risk
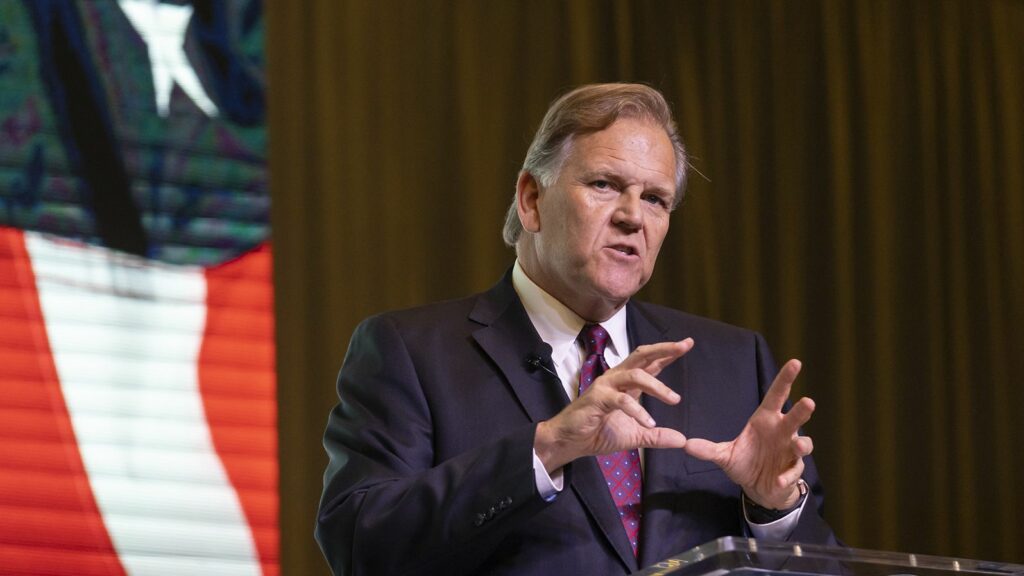
Michigan’s way of life is worth defending. That’s why I served in the Army. That’s why I served in the FBI taking down organized crime. That’s why I led the House Intelligence Committee in the hard years after 9/11.
But we can all feel that something is broken.
America under Biden and his cronies is going in the wrong direction. Our border is wide open, our justice system is broken, and Biden’s bad policies are making everything more expensive.
With your help, we’ll get America back on track. Join me in this fight.
- Mike Rogers
We can do better
Politics has gotten so small and petty, that we’re failing to address big problems. We can do better. That’s why Mike is running for the United States Senate.
Mike will fight to get government out of the way, unleash American innovation, and take common sense back to Washington. Together, we can get prices under control, secure our border, and bring good paying jobs back to Michigan.
Everything is at stake in this election. That’s why Mike needs your support. Join the team to help Mike win – contribute today:
Latest News
Perry Johnson Endorses Mike Rogers for U.S. Senate
BRIGHTON, MI — Army veteran, businessman, and Trump-endorsed candidate for U.S. Senate, Mike Rogers, announced today that he’s earned the endorsement of businessman Perry Johnson. Johnson,

Statement on Emergency Care Physician Strikes
As you cover the emergency care physician strikes today, please consider the following comment from Michigan Republican candidate for U.S. Senate, Mike Rogers: “Private equity

Alexandria Taylor Endorses Mike Rogers for U.S. Senate
BRIGHTON, MI — Army veteran, businessman, and Trump-endorsed candidate for U.S. Senate, Mike Rogers, announced today that he’s earned the endorsement of conservative leader and former